Risk Management in the Outsourcing of ICT Services in Tax Administrations

The digital transformation of tax administrations (TA) has significantly increased their dependence on specialized technological services, many of which are provided by third parties. Examples of functions often fully or partially outsourced include cloud infrastructure, core and secondary system development and maintenance, data centers, cybersecurity services, electronic invoicing, and analytical and AI-driven solutions, (especially with the use of ACPs[1]).
Suppliers are outsourced for two main reasons: to perform a job that the institution decided not to do internally and when suppliers can deliver the service more effectively or cost-efficiently than the institution itself.
While outsourcing offers benefits such as efficiency, access to specialized expertise, and scalability, it also introduces operational, technological, legal, and strategic risks—all of which require systematic management.
These risks are especially critical for tax administrations due to three structural factors
- Criticality of systems: ICT services support essential processes for TAs. An interruption can directly affect the mobilization of public resources.
- Sensitivity of information: TAs manage highly confidential tax, financial and personal data, subject to tax secrecy and data protection laws, the exposure of which can generate severe reputational and institutional damages.
- Increasing technological dependence: advanced digitalization implies that the continuity of the tax system increasingly depends on the stability and security of the technological infrastructure.
In this context, risk management for outsourced services must extend beyond contractual oversight. It should be fully integrated into the institution’s broader risk management framework, aligning with international best practices (e.g., ISO 31000, ISO/IEC 27001, COBIT, and ITIL) and the governance principles advocated by multilateral organizations.
Relevant international standards/best practices
Risk management for outsourced ICT services should be grounded in internationally recognized standards and best practices. Two of the most relevant are outlined below.
- ISO 31000 and ISO/IEC 27001[2]
ISO 31000:2018 standard (“Risk Management – Guidelines“) establishes principles, a framework, and processes for managing risk. It provides international guidelines for identifying, assessing, and mitigating uncertainties in organizations of any size. While not certifiable, ISO 31000 fosters a risk-aware culture and integrates risk management into both strategic and operational decision-making. Its principles apply to all risk management processes within a tax administration (TA).
For its part, the ISO/IEC 27001:2022 (“Information security, cybersecurity and privacy protection — Information security management systems – Requirements”) is the leading international standard for information security management systems (ISMS) and is certifiable.
Of particular relevance to this document is Annex A.5.19 (“Information Security in Supplier Relationships”), which mandates the evaluation of risks associated with third-party products and services (including cloud services) and their impact on compliance with information security requirements.
Consequently, an appropriate policy should define the segmentation of suppliers, the selection criteria, the management mechanisms, the exit strategies and the control of the associated information assets. This ensures that risks are mitigated without compromising the business objectives.
Segmentation of suppliers
In risk management, supplier segmentation involves classifying suppliers based on the level of risk and criticality they pose to the organization. This ensures that the level of control, monitoring, and contractual requirements is proportionate to the identified risk. This approach is recommended in all the standards and best practices discussed here.
Segmentation enables organizations to prioritize supervision, allocate control resources effectively, define tailored contractual requirements, and focus audit efforts.
Segmentation is usually based on five key dimensions:
- Criticality of the service
- Impact on operational continuity
- Access to sensitive information
- Technological dependence
- Financial or reputational risk
Security and other relevant aspects
According to Holloway (2025), mature organizations integrate supplier information security into a broader relationship management framework, avoiding focusing exclusively on security and incorporating aspects such as performance, continuity, regulatory compliance, sustainability, and strategic alignment.
ISO/IEC 27001 further encourages organizations to tailor supplier-related policies to specific business functions, rather than adopting a one-size-fits-all supplier management approach.
Annex A 5.19 of the standard proposes 93 controls divided into 14 categories, as summarized in Holloway (2025):
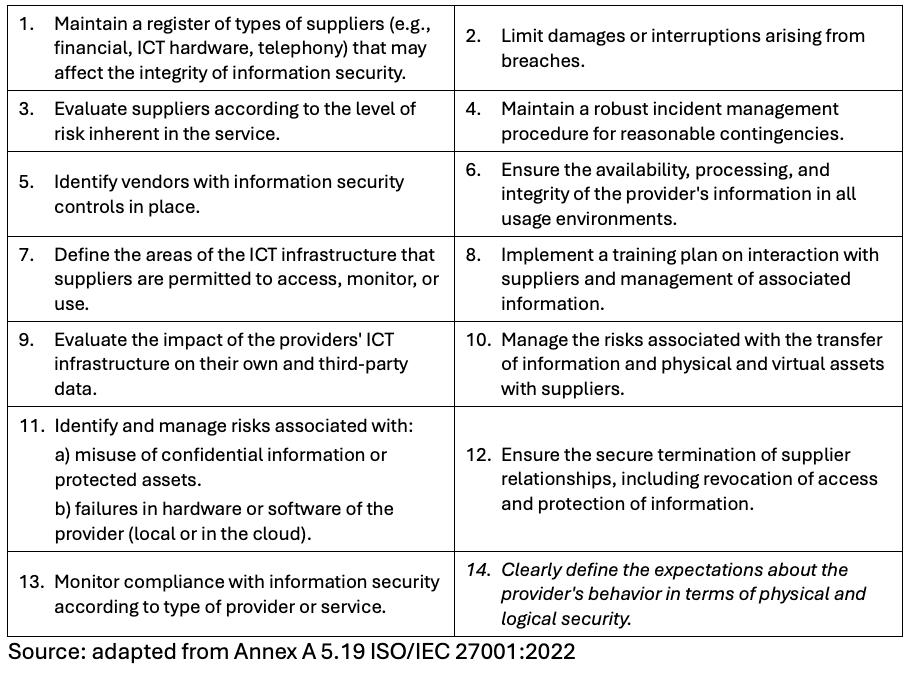
Not all controls should be applied automatically, but they should be evaluated. The recommendation is to generate a document called Declaration of Applicability (Statement of Applicability) that:
- Identify the risks (risk assessment).
- Indicates whether the control is applicable or not.
- Justifies decisions (especially exclusions).
- How it is implemented (if applicable).
An example of this document (in English), prepared for a large company, can be found at the following link: http://bit.ly/4s9STGe .
COBIT 2019:
In the COBIT framework, supplier management is addressed under the management objective APO010[3] – “Managed suppliers”, which aims to manage relationships with ICT suppliers to ensure that delivered services align with business objectives while controlling risks, costs, and performance. This objective is structured into five key management practices:
- APO010.01 – Identify and Evaluate Relationships and Contracts with Suppliers
This practice involves establishing an outsourcing and supplier management strategy that aligns with both business and ICT objectives.
It includes defining which services should be outsourced or retained in-house, establishing policies, setting selection and segmentation criteria, identifying strategic and critical suppliers, and outlining principles for contracting and governance.
Result: An institutional framework for supplier management, including a service catalog.
- APO010.02 – Select Suppliers
This practice establishes a structured evaluation and selection process, including due diligence.
It covers defining requirements, evaluating proposals (RFP/RFQ), analyzing risks, assessing technical and financial capabilities, verifying regulatory and security compliance, and selecting suppliers based on transparent criteria.
Objective: To ensure suppliers meet business and ICT requirements.
- APO010.03 – Managing relationships and contracts with suppliers
This practice maintains an effective relationships during the life cycle of the contract, ensuring flexibility in the face of business changes (especially in tax contexts).
It includes assigning managers; establishing communication; managing conflicts; coordinating activities; and fostering collaboration.
Objective: to ensure effective interaction with suppliers.
- APO010.04 – Managing the risk of suppliers
Identify and control risks associated with ICT providers, in connection with EDM03 (Risk Optimization).
It includes assessing operational and technological risks; vendor lock-in; information security; service continuity; concentration of suppliers; and integration into enterprise risk management.
Objective: to reduce the exposure to risks of outsourcing.
- APO010.05 – Monitor the performance and compliance of suppliers
Monitor compliance with agreed service levels.
It includes monitoring SLAs; evaluating KPIs; reviewing contracts; managing defaults; evaluating delivered value; and promoting continuous improvement.
Objective: to guarantee quality services aligned with the needs of the business.
Alert
Note: The APO010 management objective is complemented by APO012 – “Managed Risk”.
COBIT recommends evaluating suppliers not only based on technical compliance (e.g., SLAs) but also on the actual business value generated. For tax administrations (TAs), this could involve asking questions such as: Did the supplier’s service genuinely facilitate taxpayers in meeting their payment obligations on time?
Conclusion
ISO/IEC 27001 and COBIT approach vendor risk management from complementary perspectives. While ISO/IEC 27001 focuses on information security controls, COBIT emphasizes governance and strategic management of the ICT supplier portfolio. Together, they provide a comprehensive framework for addressing both security and operational/strategic risks associated with technological outsourcing.
Additionally, other frameworks can further enhance this approach, such as NIST SP 800-161r1 (Cybersecurity risk management practices in the supply chain) and ITIL 4 (Supplier Management” practice).
Tax administrations should also consider the growing role of Artificial Intelligence (AI) in risk management for outsourced ICT services. While AI offers significant advantages—such as automated monitoring, continuous performance evaluation, and predictive analytics, it introduces new risks that must be managed. These include ensuring transparency in AI use, controlling training data, maintaining explainability of automated decisions, and clarifying responsibility for errors or failures.
Recommended bibliography:
Aflakhah, E., Soewito, B. (2024). Assessing Information Security Using COBIT 2019 And ISO 27001:2013. Journal of System and Management Sciences. Vol. 14 (2024) No. 3, pp. 127-145. Available at: https://www.aasmr.org/jsms/Vol14/No.3/Vol.14.No.3.08.pdf
Holloway, D. (2025). ISO 27001:2022 Annex A 5.19 – Information Security in Supplier Relationships. ISMS Online. Available at: https://www .isms.online/iso-27001/annex-a-2022/5-19- information-security-supplier-relationships-2022/
Metin, B., Sevim, S., Wynn, M. (2025). Cybersecurity Strategy Development: Towards an Integrated Approach Based on COBIT and ISO 27000 Series Standards. Available at: https://www.mdpi.com/2305-6703/5/4/33
References:
[1] Summary information on the APO (Align, Plan. Organize) of COBIT 2019 can be found at: https://4matt.com.br/es/cobit-2019-alinhar-planejar-e-organizar-apo
[2] Authorized Certification Provider
[3] Available for purchase in https://www.iso.org/standard/65694.html (ISO 31000:2018) and https://www.iso.org/standard/27001 (ISO/IEC 27000:2022). The regulatory bodies of some countries provide translations or local adaptations for these standards.
2,729 total views, 2 views today